Hey you, fellow blockchain developer. If you’ve missed out our 0x06 monthly meetup which happened last week (22.01.2019) – here is some interesting stuff for you to catch up.
What happened recently
As always we discussed what interesting happened from developers perspective during the month. We got out focus on the last minute postponed Constantinople Ethereum fork.
Constantinople Ethereum fork postponed
As it turns out Chain Security, a company focused on research and security of smart contracts, found a vulnerability that might result

Summarizing this – EIP1283 which is introducing cheaper gas costs SSTORE
Contracts that increase their probability to being vulnerable are contracts that utilize a transfer() or send() function followed by a state-changing operation. An example of such a contract would be one where two parties jointly receive funds, decide on how to split said funds, and initiate a payout of those funds.
And the brief explanation: The issue is that when a CALL is made to transfer funds, even if the caller hasn’t specified additional gas, will spend 2300 gas. .transfer()
And this has not been an issue previously, because even though with 2300 gas the caller could make a CALL from the calleeSSTORE
But now after Constantinople and the EIP-SSTORE
Jump Oriented Programming in Ethereum
As the title suggests it – the whole topic that we went through is quite catchy. We initially saw this thing called Jump Oriented Programming in Ethereum last month, is quite well explained in a couple of great videos by LiveOverflow in his YouTube channel. So we got in touch with him and Milen Radkov presented this at the meetup.
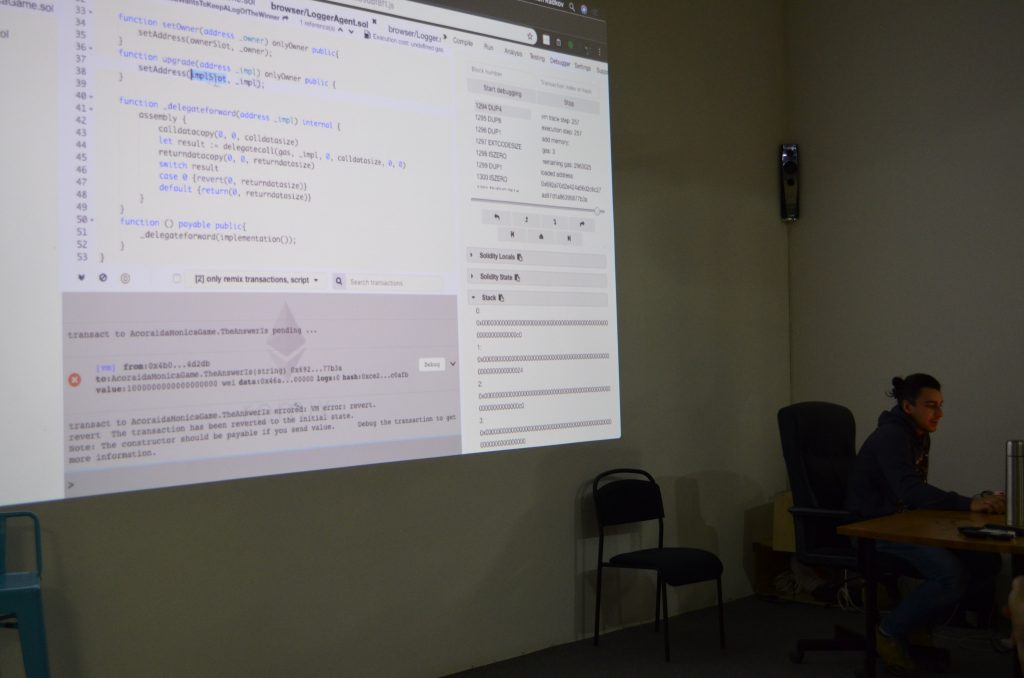
We saw how we can make a Solidity smart contract misbehave, making it acting different, hiding what exactly is it doing.
The whole thing is based on carefully selected function names, and specifically chosen address in order for the execution to succeed (in this case making it possible to withdraw and drain the whole contract).
Resources
- Github repo with all the example code
- LiveOverflow video part one
- LiveOverflow video part two
- video recording of the meetup coming soon
Useful links
Also published on Medium.