In this short tutorial I’ll be showing you how to create a fungible token on aeternity blockchain network.
In this tutorial you will create a AEX-9 (fungible token standard on aeternity) token in few easy steps.
Prerequisites:
- Waellet browser extension
Note: This will be a short tutorial on creating a fungible token with allowances.
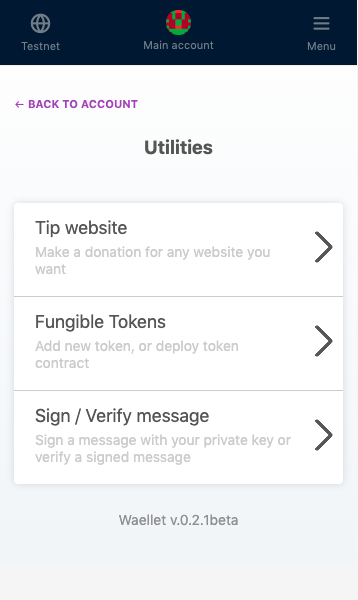
Step 1. Go to waellet Utilities section and select Fungible Tokens

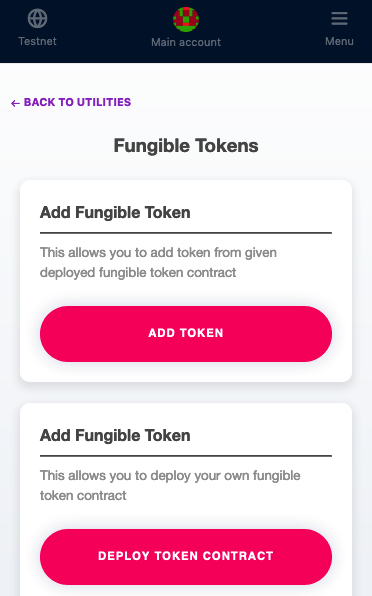
Step 2. Click Deploy fungible token button.
Step 3. Fill the form with the details needed for the token – Token Name, Token Symbol, and decimals.

Step 4. Click deploy, confirm/sign the transaction and you are ready.


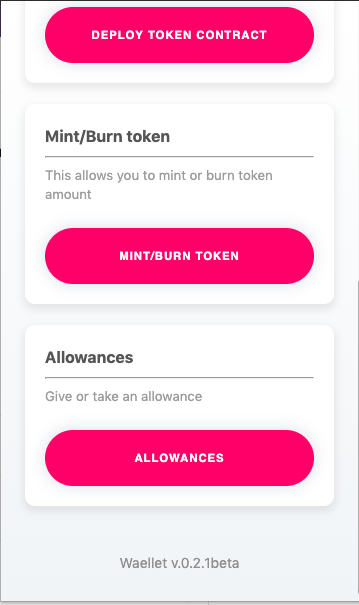
The Allowances section of waellet will allow you to interact with the contract and set allowances for addresses of your choice.
The Mint/Burn section allows us to mint (create new tokens) or burn (remove tokens from circulation) tokens.
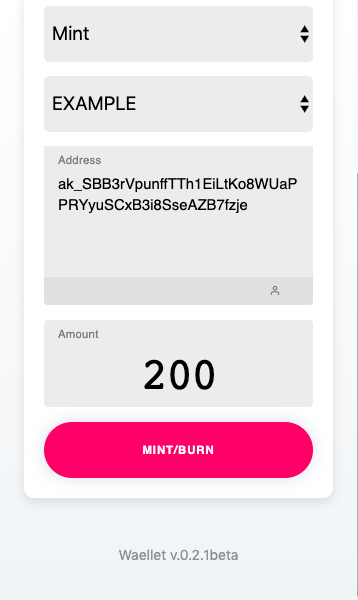
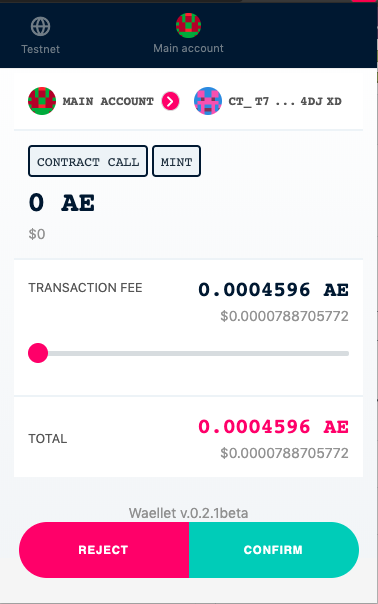
After confirming the transaction you’ve successfully minted tokens to the address you specified in the previous step.
![Cover Image for How to create aeternity fungible token? [tutorial]](/_next/image?url=https%3A%2F%2Fwp.web.hack.bg%2Fwp-content%2Fuploads%2F2019%2F10%2FScreenshot-2019-10-07-at-9.53.08.png&w=3840&q=75)


