Most blockchains function in similar ways, but one of the ways in which blockchains can differ is the way consensus is reached – which transactions are legitimate and added to the blockchain. Blockchains do this using various consensus mechanisms and in this article, we will explain the most used ones and some others.
But, first…
What is a Consensus Mechanism?
The technology behind consensus mechanisms is based on a theoretical problem outlined by computer scientists in 1982. The Byzantine Generals’ Problem asks whether it is possible to form a consensus in a computer network composed of independent, geographically distributed nodes, and consensus mechanisms present the answer.
Blockchain solutions run in the form of networks that allocate equal access and rights to all computers in the network with the purpose to reach an agreement on the same value. In a full decentralized solution, the nodes (every computer on the network is referred to as a peer or node) communicate directly with each other and no peer or node has more power than other peers or nodes. Therefore, a blockchain does not have coordinators, directors, or managers for enforcing rules and determining and punishing unacceptable behaviour. On the contrary, the system depends on a mechanism implying that all nodes follow similar rules or protocol for reaching the agreement.
Consensus is the term used when there is an agreement among all nodes, and it literally means ‘general agreement.’ Consensus is the most important but difficult task in a decentralized system without any authorities. A major share of nodes should agree on the truth or validity of information or transactions, thereby ensuring the proper functioning of the system and weeding out invalid transactions.
This action is successfully achieved by following predefined rules set out in the consensus mechanisms. First, every mechanism should enable the network to reach an agreement, without allowing individual parties to act in their own interests above those of the network, incentivizing parties to play by the rules.
Not only that, for a transaction to be successfully registered on the ledger and added to a block, consensus needs to be achieved between all nodes. The equal distribution of responsibility across node operators ensures that the consensus mechanism continues to function successfully, even in the event of one or more nodes failing to accomplish their tasks (whether deliberately or accidentally).
These two rules are generated from the Byzantine Fault Tolerance consensus mechanism which aims to reduce the influence of the faulty nodes in the network.
Another critical challenge is time. Obtaining consensus between hundreds or even thousands of network participants isn’t necessarily a fast process. Ever since the first blockchain was launched back in 2009 – Bitcoin Blockchain, developers have proposed various alternatives for achieving consensus and dealing with the time obstacle.
If you want to read more about this problem, check out our article on the subject.
Simply put, there’s no consensus on consensus. Rather, there are a variety of methods in use today, and every one of them has its unique pros and cons. In this article, we are going to address the two most used ones – Proof of Work and Proof of Stake as well as mention some others.
Proof of Work (PoW)
Bitcoin is the first application built on blockchain technology, in which all participating computers (“nodes”) store a copy – or, more precisely, a replica, since there is no distinguished master – of the associated ledger. A ledger is commonly defined as a collection of accounts, stating one’s current rights of ownership of a particular asset – in the case of Bitcoin, units of the eponymous cryptocurrency. The underlying technology, blockchain, provides a means to store information chronologically and redundantly on a decentralized database, and an agreement process through which the nodes synchronize and modify their global state.
Blockchains, in general, achieve this synchronization by linking transactions to form batches (“blocks”) and adding these, sequentially, to the existing linear data structure (“chain”). Utilizing Merkle trees and hash-pointers, this data structure is highly tamper-sensitive, making retrospective manipulations easy to detect.
Anyone can run a node for the common cryptocurrencies and participate in the consensus mechanism of their underlying blockchains using public-key cryptography and hence without any form of registration. Consequently, blockchains underlying such open systems, which allow for unrestricted access and participation, are termed permissionless. Since, on a permissionless blockchain, the inclusion of a distinct entity to provide accounts and passwords is not viable, authentication based on public key infrastructure is highly suitable.
For such blockchains, a simple voting-based agreement process based on “one man – one vote” is not secure, since a potential attacker could simply create multiple accounts to gain a majority and take control of the system – this is called a Sybil attack.
Bitcoin’s key innovation was to provide a suitable consensus mechanism for use in this scenario. Bitcoin combined several well-known concepts from cryptography to form the so-called Proof of Work (PoW) consensus mechanism. This refers to the right to create a new block from a subset of queued transactions when one finds a solution to a cryptographic, computationally intensive puzzle (that is in some way meaningful for business or science). The process of searching for a solution is called “mining” and the network operators -“miners”. This results in coupling the voting weight to a scarce resource – computing power and thus energy – and hence prevents Sybil attacks.
Miners work by competing to become the first to solve a computational puzzle known as a hash, which takes all of the most recent unconfirmed ledger transactions as an input. The hash puzzle is asymmetric, meaning it’s difficult to solve, but quick and easy to verify if the solution is correct. The miner who solves the hash puzzle mines a block of transactions and presents their solution to the network for verification. If it passes the verification, the block is added to the blockchain, and the miner is rewarded for every valid block that is found and disseminated. The reward typically consists of a certain amount of the associated cryptocurrency and the fees for the associated transactions. The value of the former is proportional to the cryptocurrency’s market price, so the success of cryptocurrencies on financial markets in the last years has provided a very strong incentive to participate in mining.
The PoW mechanism is highly secure. Bitcoin has been running for 12 years now, and the network has yet to be compromised. This inherent security is well-suited to a financial ledger, which is why so many cryptocurrencies adopt PoW. However, it comes with the significant challenge of being highly inefficient. First of all, the process of solving the hash puzzle takes several minutes. Because Bitcoin has a fixed block size of 1MB, this limits the network to a processing speed of around 4–5 transactions per second, compared to the Visa network which processes an average of 1,700 transactions per second.
Another drawback to this consensus mechanism uses a lot of resources which turns out to be energy-inefficient.
According to Statista, bitcoin’s average energy consumption per transaction (as of August 16, 2021) is 1 722.24 kilowatt-hours, compared to that of 100 000 Visa transactions – 148.63 kWh.
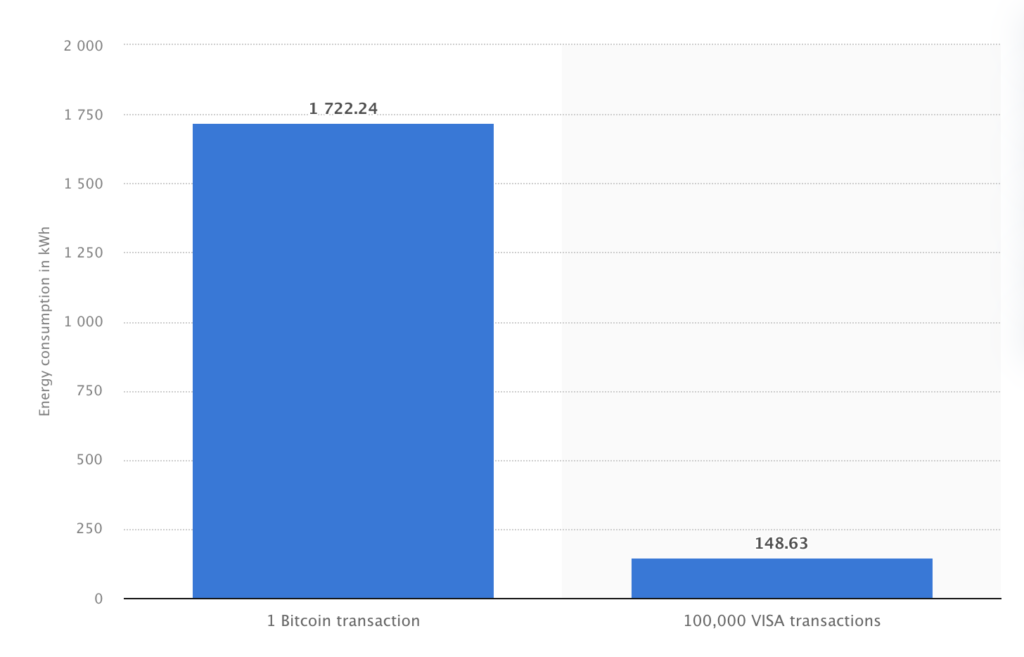
These statistics show why some blockchains are moving to different consensus mechanisms.
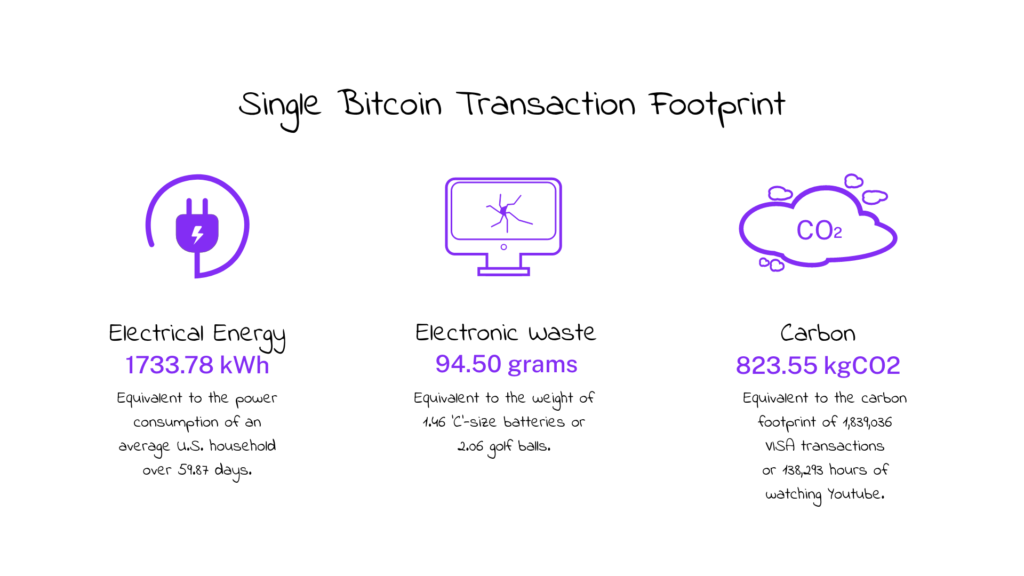
At first glance, the numbers might seem concerning but one has to ask themselves the question of how much the security of a new generation of payment – one trustless, decentralized, and censorship-resistant is worth? The more energy spent in PoW – the more inherent security is added to the system.
Proof of Stake (PoS)
The PoW is not the only way to achieve consensus in a distributed system. The probably best-known alternative for the permissionless systems required for cryptocurrencies and other open decentralized applications is the so-called Proof-of-Stake (PoS) consensus mechanism.
In this case, the weight of a participant’s vote is not tied to the scarce resource of computing power, but to the scarce resource of capital.
More precisely, there is a random mechanism that determines who is allowed to build (“mint”, “forge”, “bake”) and attach the next block. With the help of this mechanism, the probability of being selected is linked to the amount of cryptocurrency that the node has deposited and locked (staked) for this purpose. The deposit also incentivizes the node to stick to the rules of the network, as any misbehaviour detected will lead to the node losing this deposit.
The process that decides who gets to produce the next block takes a couple of factors into account, what these factors depend on the design of the blockchain, but in general, the person who has the biggest stake has the highest chance to produce a block. Another factor that can be taken into account is how long the coins have been staked.
Validators are also rewarded for their work. The reward that the validator receives for creating the next block depends on the design of the blockchain yet again. Usually, they either receive all, or part of, all the transaction fees of all the transactions in the block they created, or they receive a fixed amount of coins.
The advantage of PoS is that it does not involve any computationally intensive steps such as solving the cryptographic puzzles and is the more environmentally friendly brother of the Proof Of Work protocol.
Proof Of Stake is not only much more energy-efficient than the Proof Of Work system, but it also has another major distinction. In a Proof Of Work system, a miner may own none of the coins they are mining, meaning they only seek to maximize their profits without actually improving the network. In a Proof Of Stake system validators have a much bigger incentive to actually maintain the network as they actually hold the coins of the blockchain on which they are validating meaning that those who own coins in a network have a vested interest in keeping the network maintained and the value of its coins high.
A variation of the PoS mechanism, worth mentioning is the so-called Delegated Proof-of-Stake (DPoS) system. Participants still stake coins, but rather than becoming responsible for validation themselves, stakeholders outsource that work to delegates — groups that are then responsible for reaching consensus between themselves to validate the next block. These delegates are elected based on their reputation and trustworthiness and are also called witnesses or block producers. A limited number of delegates (most systems choose between 20 and 100) are chosen for each new block, so the delegates of one block might not be the delegates of the next.
According to some, DPoS is a more democratic way of choosing who verifies the next block, allowing a more diverse group of people to participate in the process since it’s based on earned reputation as a legitimate staker and not overall wealth. Furthermore, because there are a limited number of validators, DPoS allows the network to reach consensus more quickly making it faster than PoS and PoW consensuses.
Other Types of Consensus Mechanisms
Besides PoW and PoS, there are other kinds of consensus mechanism algorithms, each of which works on different principles, but since many of these types of consensus mechanisms are not currently used in real-life applications, we will not investigate them in detail.
Proof of Authority (PoA) – It operates in a similar way to PoS, except that rather than staking tokens, those in the network stake their own reputation. The underlying principle is that if they prove to be unreliable, they lose their authority and can no longer produce or validate blocks.
Proof of Capacity (PoC) – A consensus mechanism algorithm used in blockchains that allows for mining devices in the network to use their available hard drive space to decide mining rights and validate transactions. This is in contrast to using the mining device’s computational power (as in the PoW algorithm).
Proof of Burn (PoB) – It is an alternative consensus algorithm that tries to address the high energy consumption issue of a PoW system. PoB is often called a POW system without energy waste. It operates on the principle of allowing miners to “burn” virtual currency tokens. They are then granted the right to write blocks in proportion to the coins burnt.
Conclusion
This list isn’t exhaustive, but it covers the basic principles of the consensus models typically used by the main public blockchains. In conclusion, there is no “best” consensus mechanism that serves all business models at this moment. A business looking into which mechanism is best for their needs should consider the various factors that correspond to their products or services.
Opting to build your system on a fixed blockchain with a certain consensus mechanism can present some risks you should consider.
At the end of the day, there is no one-size-fits-all solution, but, by understanding the various consensus processes and their tradeoffs, you can make a well-informed decision.
If you have any questions regarding consensus mechanisms or other blockchain topics, drop us a message.



